Should I Use SAST or DAST?

Cybersecurity is an important concern in the modern era. With the rise of smart devices and continuous advancements in the field of technology, precautionary measures must be taken in order to maintain the overall stability of these devices. Hence, several methods for testing are employed to deduce any kind of abnormal activity or occurrence in these technological innovations.
Most companies and industries are investing their valuable resources to prevent external forces from interfering with the natural working activities of their internal devices. The two main application security testing measures used for this purpose by industries are static application security testing (SAST) and dynamic application security testing (DAST).
In this article, we will try to break down both of these aspects individually. First, we will give you a brief introduction of SAST and then proceed to understand the numerous aspects of DAST. Finally, we will arrive at a conclusion on which of these two application security measures is best suited for your particular tasks.
Static Application Security Testing
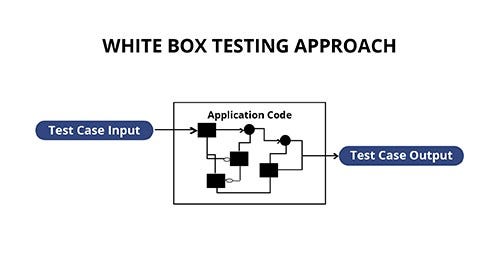
SAST is often referred to as a method of white-box security testing.
It is used to secure software and other internal features by reviewing the in-depth binary or source codes of the available software and identifying the main sources of vulnerabilities. This method of application security testing has existed for a long time but gained more popularity during the 1990s.
To understand the true meaning behind this statement, let us look at some of its features. SAST allows the user to access the internal and underlying frameworks, designs, and implementations. The application is tested from the inside out. This type of testing represents the developer approach.
SAST utilizes and requires the source code for analysis. This statement basically means that SAST does not require a deployed application. It analyzes the numerous source codes or the binary transformation without actually executing the application.
The main advantages of using SAST are that you can find vulnerabilities and fix them faster during the systems development life cycle (SDLC) phase. Numerous SAST scans can be run during the phase when the feature cycle is considered complete. Since most issues can be fixed during this time, i.e. before the deployment stage, SAST is deemed as a less expensive method in comparison to other testing methodologies.
Apart from SAST being fairly cheap, it also has one more significant advantage. SAST is typically supportive of all kinds of software in the industrial applications department.
However, one of the major drawbacks of SAST is that they cannot discover run-time and environment-related issues that occur. The main reason for their inability to detect such issues is that SAST scans static code and it cannot discover run-time vulnerabilities.
Dynamic Application Security Testing
A DAST is a type of black-box security testing methodology.
It is basically a tool that is utilized in a program that can communicate with a web application or other web interfaces through the front-end. Using this technique, the DAST can be useful in identifying potential security vulnerabilities in the web application and architectural weaknesses.
The tester in DAST usually has no additional information or knowledge of the technologies or frameworks on which the application is built. The approach for testing in DAST is from the outside in, as that is how potential hackers would attack the system. Therefore, this type of testing is usually conducted by ethical hackers.
The main advantage of using a DAST is that it does not require any kind of source code or binaries. The analysis is always performed during the execution phase of the application. Unlike SAST, it can also discover other run-time and environment-related issues. While static applications cannot perform this task, it is easily possible for a dynamic application to perform such tasks.
However, DAST also has a few issues. It finds vulnerabilities towards the end of the SDLC phase. Since these bugs and vulnerabilities can only be discovered after the development cycle is complete, the overall procedure is longer and expenditure is more. Hence, it costs more to do DAST.
When vulnerabilities are found towards the end of the SDLC phase, the delivery and deployment of the product also need to get pushed a bit further. Also, DAST typically scans only apps like web applications and web services. Unlike SAST, they are not useful for other types of software.
Conclusion
While both SAST and DAST have their own unique features and for certain applications, they can be considered more suitable for testing purposes, a slight preference is usually given to SAST methods.
But, it is worth noting that both these techniques complement their respective counterparts. Performing both of these security testing measures can be carried out for more concise and comprehensive testing.
Cybersecurity is an increasing concern for the current generation. Hence, it is extremely crucial to protect your devices and technical equipment from malicious activities. Therefore, ensuring a security application testing software or tool is used for securing these devices is an essential step for the manufacturing of any technological product.