Best Practices for Kubernetes Development
In this article, I'll go over some of the finest Kubernetes deployment strategies.
Introduction
Continuous integration and continuous deployment (CI/CD) are critical as systems become more automated. Since so many enterprises use its services in production, Kubernetes has a big place in implementing CI/CD in the form of containerization. When applications are deployed in production, they require rapid pattern changes. This is where "containerization" comes in handy.
Kubernetes is acquiring a lot of popularity as a result of its qualities. In this article, I'll go over some of the finest Kubernetes deployment strategies. Let's take a look at each one separately.
Best Practices for Deployment
Keep control of your deployment with request restrictions
Although Kubernetes can scale itself automatically, the administrator must ensure or keep a watch on deployment to ensure that it has sufficient resources. If the deployment does not have sufficient resources, the CrashLoopBackOff error may occur. Admins may easily spin up more copies and make effective modifications at the CPU or RAM level because it is so simple. On a CPU and memory level, requests and constraints are utilized to manage resources.
Requests are resources that a container requires or that are only granted when a container makes a request for them.
Limits and restrictions are the same things because a container will not accept anything that exceeds its capacity. As a result, it will be unable to take advantage of many of the resources available to an organization.
Note: Kubernetes will give a CrashLoopBackOff error if the limit is less than the request. Each container in a pod has its own requests and resource limitations, but because pods are scheduled in groups, admins must specify the “requests” and “limits” values so that they can work together to achieve a pod average value.
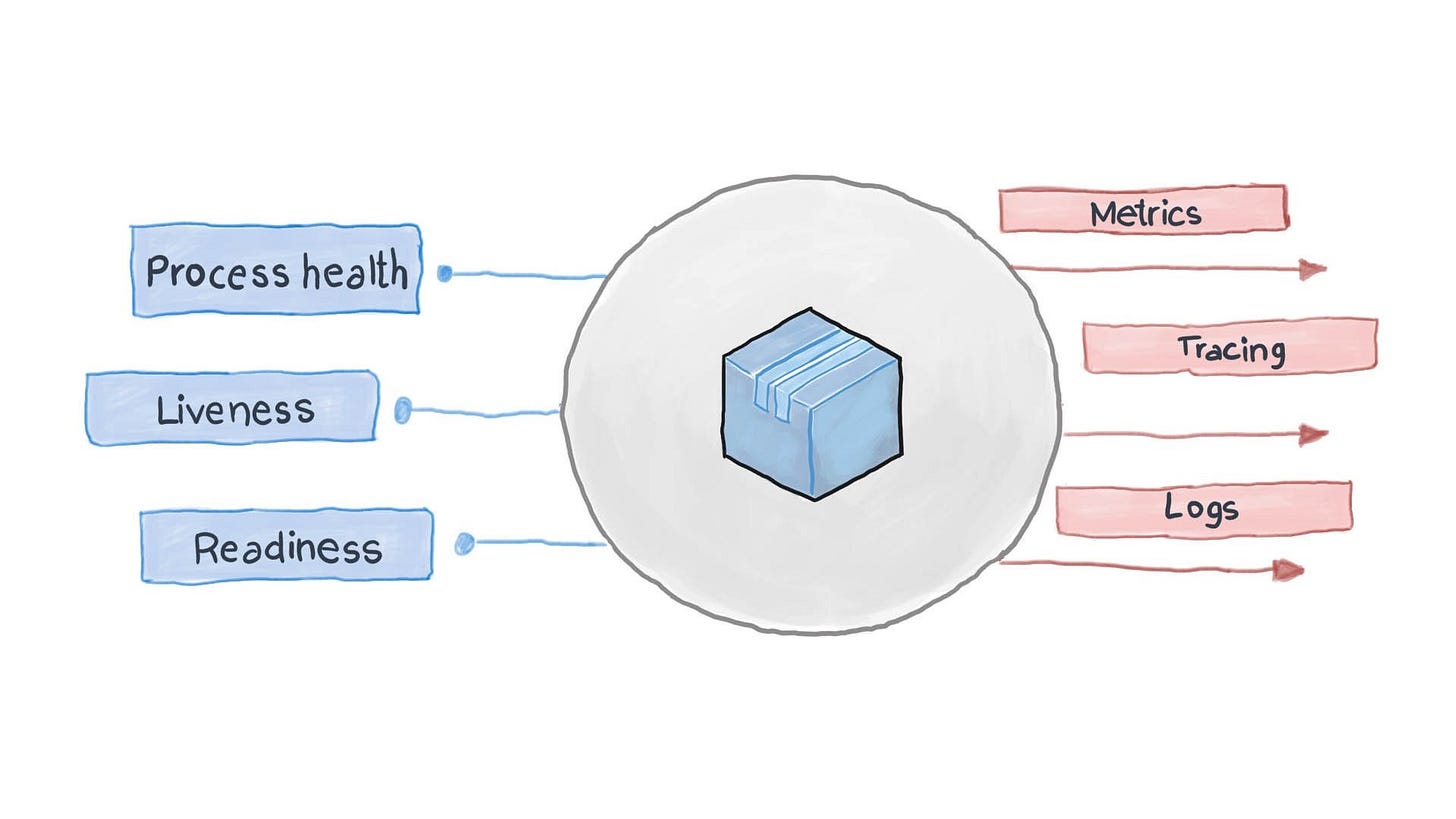
Perform health checks with readiness and liveness probes
Kubernetes "health checks" are critical because they give performance, storage, and other reports that can help you enhance your Kubernetes' health.
After decreasing operational difficulties, Kubernetes liveness and readiness probes assist in making services more robust and resilient. Liveness simply refers to how quickly a container can be restarted, whereas readiness refers to how quickly the container is ready to handle traffic.
Liveness probes’ values are not the same as readiness probes’ values. Additionally, liveness probes are configured in passive mode, while readiness probes are configured in active mode. If a fatal error occurs, the container may crash. Therefore, be cautious and never elevate it in that situation.
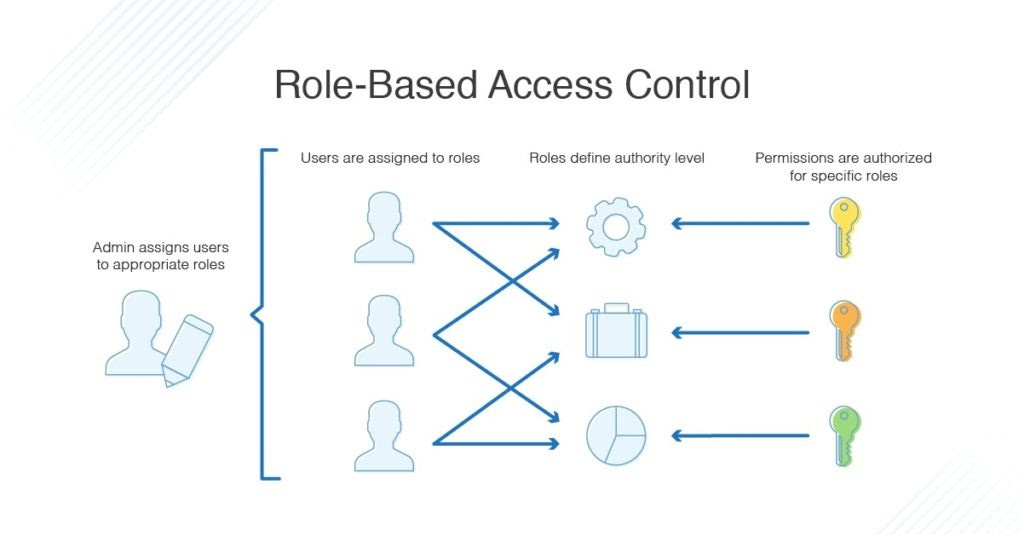
Enable role-based access control (RBAC)
RBAC restricts user access based on their organizational role. The limits of a normal user differ from those of an administrator. Kubernetes administrators have the same ability to define who can execute what on the Kubernetes cluster by setting permissions based on roles and rules.
Admins must set the “Role” and “ClusterRole” parameters in Kubernetes to enable RBAC. Roles grant access to a particular namespace resource. Permission to access a cluster-wide resource is granted by ClusterRole.
RBAC referencing is also supported, implying that a "Role" can refer to a “ClusterRole” and bind that ClusterRole to the role bindings namespace.
Note: RBAC can be applied to a single person or a group of people.
Resource utilization
To successfully execute Kubernetes, the administrator must specify some resource limits. There are several fundamental guidelines for improved resource use, such as do not set CPU restrictions unless you have a good use case, set CPU requests to one CPU if required, or set CPU requests to below one if practicable. Admin can establish the right quality of service (QoS) for pods and LimitRange for the namespace.
Keep small container images
Users in Kubernetes can develop and utilize images, but most of the time, they use the base images, which already contain many of the packages and libraries required for this configuration or resource.
Always prefer to use a light image—one with fewer packages—as this speeds up builds and decreases the risk of malware and viruses being carried inside the image. When choosing an image, the user should choose “ALPINE” pictures, which are 10 times lighter or smaller than the base images, and then add the libraries and packages that the program requires.
Both approaches aid in the creation of light pictures, which are always less vulnerable to attacks due to their lower attack surface area.
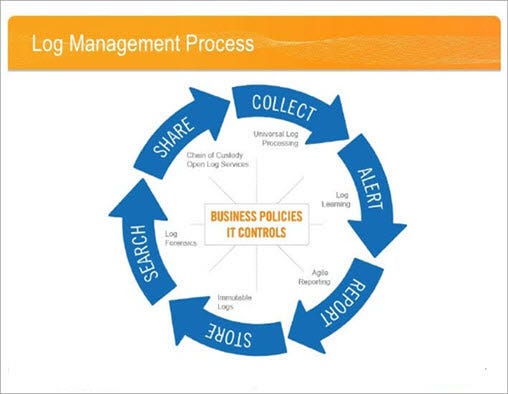
Regular review of policy logs
When a user completes a job on Kubernetes, a log is written to show that the work was completed by that user. Policy logs must be monitored on a regular basis by administrators to understand how policies are being used and where policy modifications are required.
At this location, all audit logs are saved as /var/log/audit.log. The purpose of a log audit is to discover threats to resources, resource consumption, and the heartbeats of the Kubernetes cluster.
When an administrator installs Kubernetes, it comes with predefined default policies, such as /kubernetes/audit-policy.yaml files, which can be customized to meet the needs of their organization. Admins can check the policy manually or with the help of a program. There are other programs available for this purpose, including “Fluentd,” an open-source utility.
Conclusion
As we all know, Kubernetes is quite popular. Thus, implementing it while following some best practices will yield more successful outcomes. We discussed some recommended practices from my experience in this article, but they may alter depending on your cluster architecture. Each application's built structure is unique and demands a unique approach to fine-tuning. The only thing that matters at the end of the day is how to optimize your containerized framework.